NeroSwarm Honeypot
Overview
NeroSwarm Honeypot is a Deception-as-a-Service platform designed to deploy decoy systems across networks. By detecting and monitoring malicious activity at the earliest stages of an attack, NeroSwarm lures adversaries into revealing tactics and techniques before critical assets are reached. This approach significantly reduces false positives and alert fatigue, providing security teams with real-time, high-fidelity insights into internal threats.
- Vendor: NeroSwarm Honeypot
- Supported environment: SaaS
- Detection based on: Alerts
- Supported feature: Events associated with incidents
Step-by-Step Configuration Procedure
Create an Intake
- Navigate to the Intake page in Sekoia.io.
- Click Create Intake and select NeroSwarm from the dropdown.
- Copy the generated Intake Key (this key is required in the next section).
Configure NeroSwarm to Forward Logs
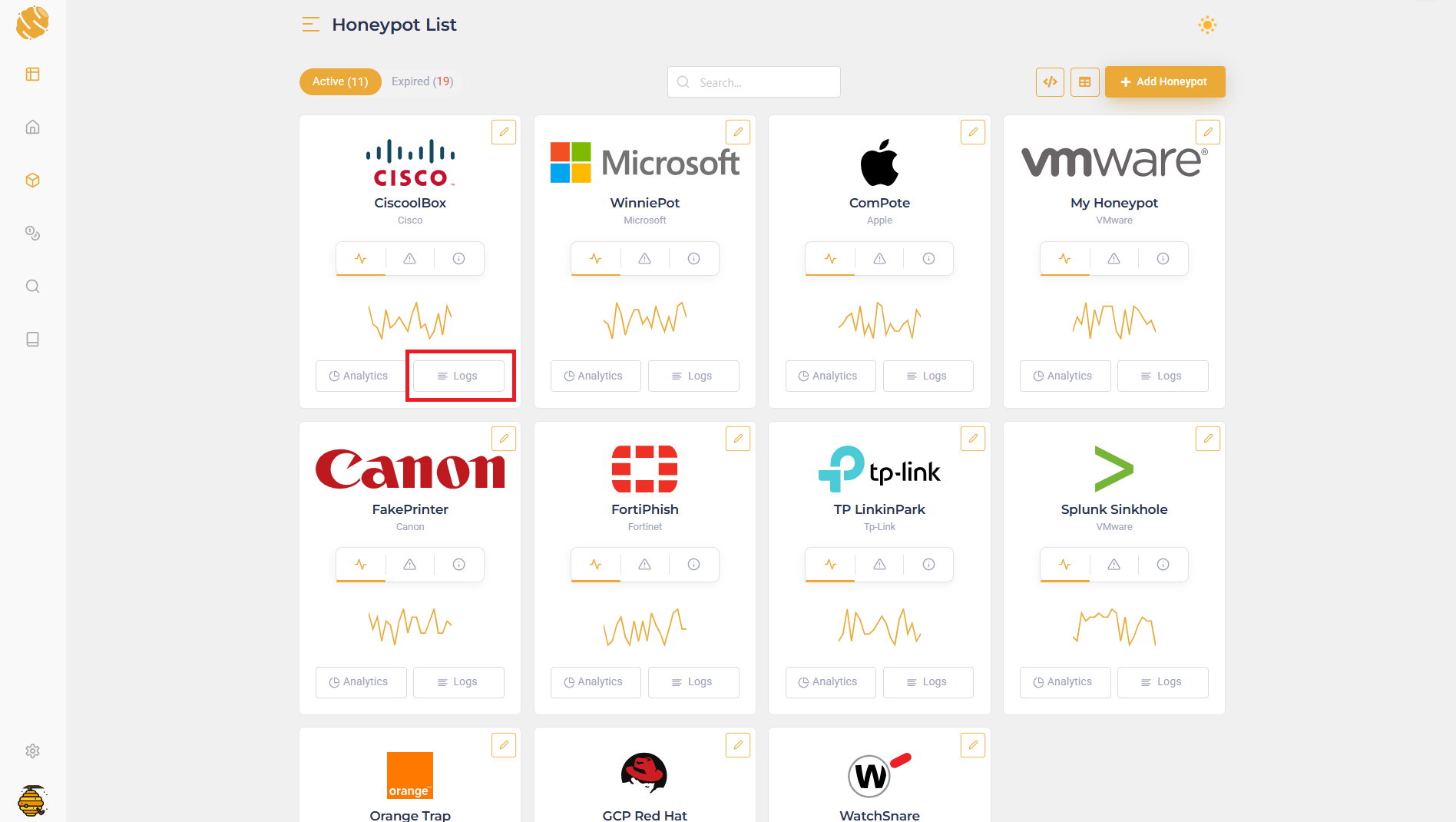
- Log in to the NeroSwarm Honeypot dashboard.
-
From the Honeypot List, click Logs for the honeypot to integrate.
-
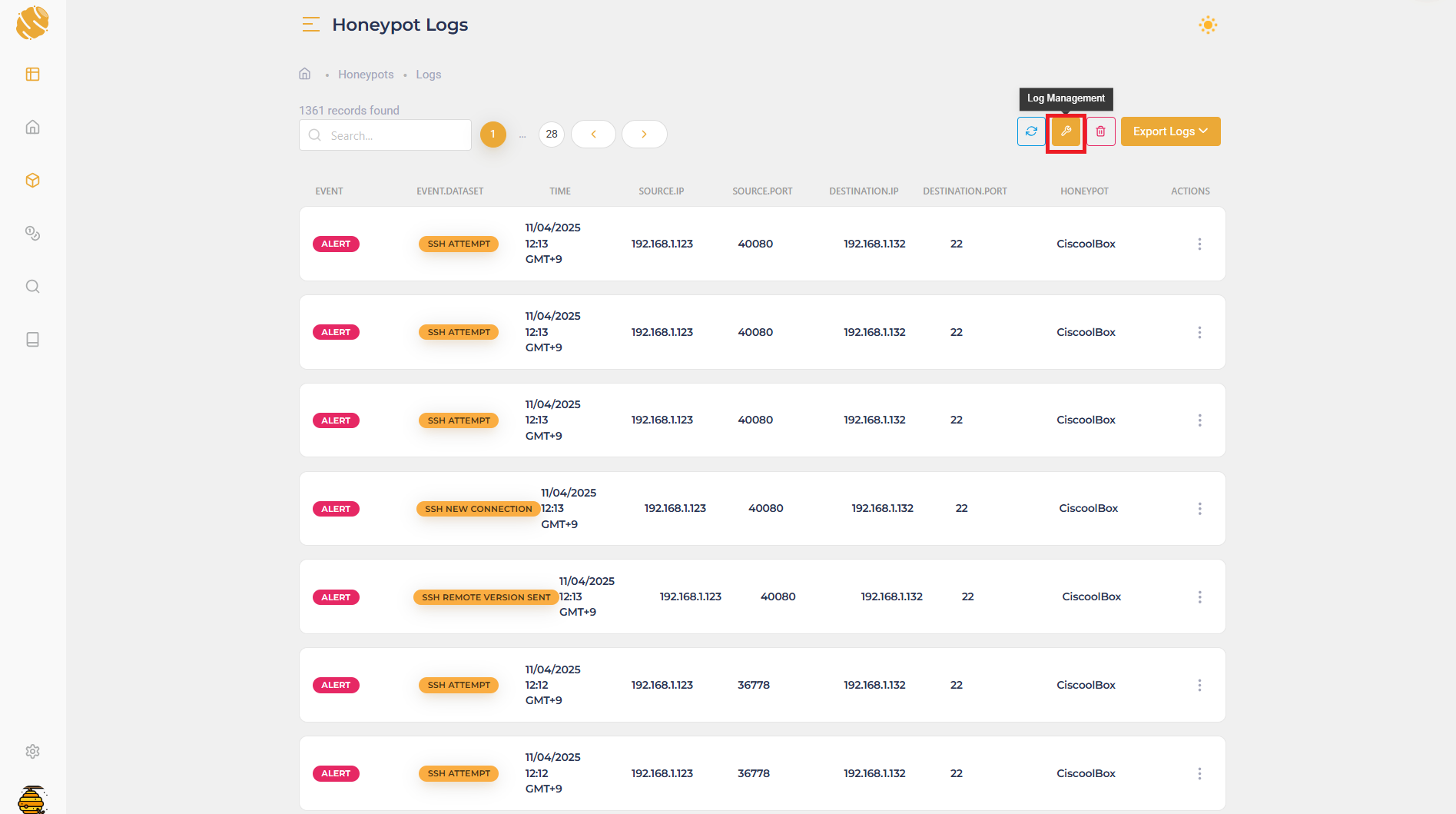
In the Log List, click Log Management.
-
In the Log Management modal:
- Select Sekoia.io from the integration options.
- Paste the Intake Key obtained earlier.
- Click Confirm to save changes.
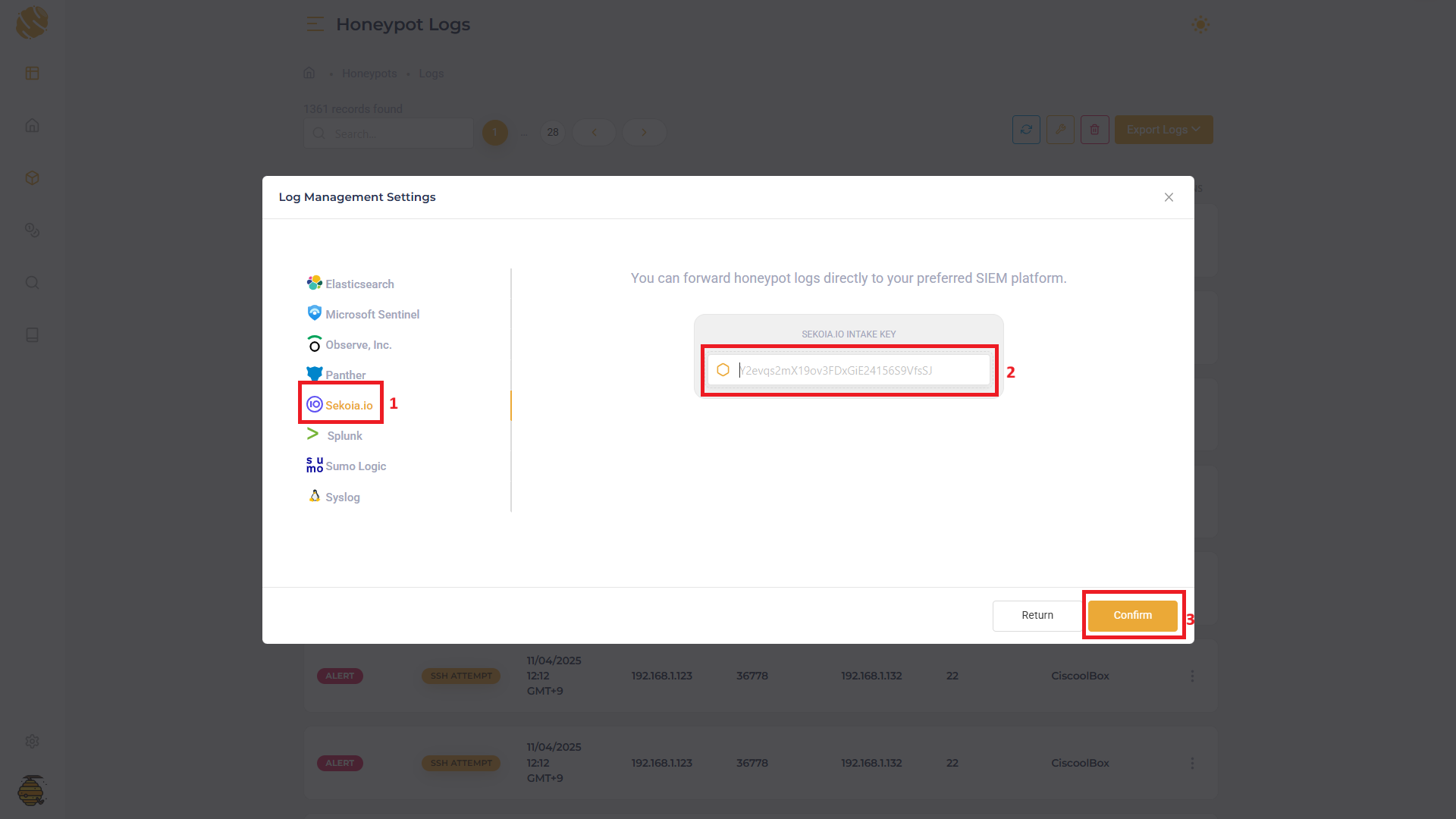
Note: It takes around 2 minutes for the changes to be reflected.
Verify Inbound Events
Once the configuration has propagated (about 2 minutes later), navigate to the Events page in Sekoia.io. Incoming events from NeroSwarm will appear here, ready for investigation and advanced threat correlation.

Raw Events Samples
In this section, you will find examples of raw logs as generated natively by the source. These examples are provided to help integrators understand the data format before ingestion into Sekoia.io. It is crucial for setting up the correct parsing stages and ensuring that all relevant information is captured.
{
"time": 1748052015,
"host": "CiscoolBox",
"source": "HTTP_GET",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"user_agent": {
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36"
},
"client": {
"ip": "192.168.1.212",
"port": 56419,
"geo": {
"continent": null,
"country": null,
"country_iso": null,
"city": null,
"postal": null,
"timezone": null,
"as_domain": null,
"as_name": null,
"asn": null,
"city_geoname_id": null,
"city_iso": null,
"continent_geoname_id": null,
"country_geoname_id": null,
"accuracy_radius": null,
"location": {
"lon": null,
"lat": null
}
}
},
"server": {
"ip": "192.168.1.132",
"port": 443
},
"url": {
"path": "/login"
},
"http": {
"request": {
"method": "GET",
"referrer": null,
"headers": {
"useragent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36",
"language": "en-US,en;q=0.7"
}
},
"response": {
"status_code": "200"
}
},
"tls": {
"version_protocol": "http/1.1"
},
"user": {
"name": null
},
"credential": {
"compromised": null
},
"session": {
"id": "518b913f3cf61879"
},
"language": "en-US,en;q=0.7",
"logtype": 3000,
"tracking_id": "eb2ab4dcad5bfa9908be7f29da14aa81d0f84e8a3cf9396deb477171cd7ca60e",
"template": "openwrt",
"action": "connection",
"protocol_name": "TCP",
"protocol_number": "6",
"vulnerability": {
"id": null,
"description": null
},
"cmd": {
"list": null
},
"crawler": {
"bot_name": null,
"bot_category": null
},
"file": {
"upload_file": null,
"mime_type": null,
"size": null,
"hash": {
"sha256": null
}
},
"dns": {
"type": null,
"ip": null,
"nameserver": null,
"alias": null,
"mname": null,
"rname": null,
"serial": null,
"refresh": null,
"retry": null,
"expire": null,
"minimum": null,
"pointer": null,
"exchange": null,
"preference": null,
"text": null
},
"ssh": {
"local_version": null,
"remote_version": null,
"incoming_packet_sequence": null,
"outgoing_packet_sequence": null,
"keyalg": null,
"login_attempts": null,
"auth_method": null
},
"sql": {
"client_encoding": null,
"database": null,
"thread_id": null,
"hash_type": null,
"salt": null
},
"vnc": {
"client_response": null,
"client_version": null,
"encryption_type": null,
"server_challenge": null
},
"rdp": {
"client": null,
"cookie": null,
"mstshash": null
},
"ntp": {
"request_type": null,
"request_mode": null,
"request_version": null
},
"sip": {
"headers": {
"allow": null,
"call-id": null,
"contact": null,
"from": null,
"cseq": null,
"max-forwards": null,
"to": null,
"via": null,
"user-agent": null,
"content-type": null,
"accept": null
},
"error": null
},
"snmp": {
"version": null,
"community_string": null,
"pdu_type": null,
"request_id": null,
"variable_bindings": null
},
"tftp": {
"filename": null,
"opcode": null,
"mode": null
},
"git": {
"repo": null,
"host": null
},
"mitre": {
"tactic": "Discovery",
"technique": "File and Directory Discovery",
"id": "T1083"
},
"raw_data": {
"post_data": null
},
"related": {
"ip": [
"192.168.1.212",
"192.168.1.132"
],
"user": [
null
]
}
}
}
{
"time": 1748073000,
"host": "CiscoolBox",
"source": "NTP_REQUEST",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "148.170.245.211",
"port": 33372,
"geo": {
"continent": "Europe",
"country": "Belgium",
"country_iso": "BE",
"city": "Brussels",
"postal": "1000",
"timezone": "Europe/Brussels",
"as_domain": "easyhost.be",
"as_name": "Easyhost BVBA",
"asn": "AS28747",
"city_geoname_id": 2800866,
"city_iso": "BRU",
"continent_geoname_id": 6255148,
"country_geoname_id": 2802361,
"accuracy_radius": 20,
"location": {
"lon": 4.347,
"lat": 50.8534
}
}
},
"server": {
"ip": "0.0.0.0",
"port": 123
},
"session": {
"id": "7f08bb08f3c54ba"
},
"logtype": 11001,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"action": "connection",
"protocol_name": "UDP",
"protocol_number": "17",
"ntp": {
"request_type": "Symmetric Active",
"request_mode": "1",
"request_version": "3"
},
"mitre": {
"tactic": "Reconnaissance",
"technique": "Active Scanning",
"id": "T1595"
},
"related": {
"ip": [
"148.170.245.211",
"0.0.0.0"
],
"user": []
}
}
}
{
"time": 1748073209,
"host": "CiscoolBox",
"source": "POSTGRES_LOGIN_ATTEMPT",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "8.98.145.113",
"port": 55086,
"geo": {
"continent": "North America",
"country": "United States",
"country_iso": "US",
"timezone": "America/Chicago",
"as_domain": "amazon.com",
"as_name": "Amazon.com, Inc.",
"asn": "AS14618",
"continent_geoname_id": 6255149,
"country_geoname_id": 6252001,
"accuracy_radius": 1000,
"location": {
"lon": -97.822,
"lat": 37.751
}
}
},
"server": {
"ip": "192.168.1.132",
"port": 5432
},
"user": {
"name": "postgres"
},
"credential": {
"username": "postgres",
"password": "postgres",
"compromised": true
},
"session": {
"id": "b6f6512185e4064d"
},
"logtype": 20001,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"action": "login",
"status": "success",
"protocol_name": "TCP",
"protocol_number": "6",
"sql": {
"client_encoding": "UTF8",
"database": "postgres"
},
"mitre": {
"tactic": "Persistence, Initial Access",
"technique": "Valid Accounts",
"id": "T1078"
},
"related": {
"ip": [
"8.98.145.113",
"192.168.1.132"
],
"user": [
"postgres"
]
}
}
}
{
"time": 1748075181,
"host": "CiscoolBox",
"source": "RDP_LOGIN_ATTEMPT",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "152.111.92.207",
"port": 60892,
"geo": {
"continent": "Asia",
"country": "South Korea",
"country_iso": "KR",
"timezone": "Asia/Seoul",
"as_domain": "uplus.co.kr",
"as_name": "LG DACOM Corporation",
"asn": "AS3786",
"continent_geoname_id": 6255147,
"country_geoname_id": 1835841,
"accuracy_radius": 200,
"location": {
"lon": 126.9741,
"lat": 37.5112
}
}
},
"server": {
"ip": "192.168.1.132",
"port": 3389
},
"user": {
"name": "admin"
},
"credential": {
"username": "admin",
"password": "windows123",
"compromised": false
},
"session": {
"id": "5a385f4d044f7c0f"
},
"logtype": 14003,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"domain": "prod",
"action": "login",
"status": "failed",
"protocol_name": "TCP",
"protocol_number": "6",
"rdp": {
"client": "remina"
},
"mitre": {
"tactic": "Credential Access",
"technique": "Brute Force",
"id": "T1110"
},
"related": {
"ip": [
"152.111.92.207",
"192.168.1.132"
],
"user": [
"admin"
]
}
}
}
{
"time": 1748070903,
"host": "CiscoolBox",
"source": "SSH_LOGIN_ATTEMPT",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "158.94.46.176",
"port": 41958,
"geo": {
"continent": "Asia",
"country": "Malaysia",
"country_iso": "MY",
"city": "Klang",
"postal": "41700",
"timezone": "Asia/Kuala_Lumpur",
"as_domain": "tm.com.my",
"as_name": "TM TECHNOLOGY SERVICES SDN. BHD.",
"asn": "AS4788",
"city_geoname_id": 1732905,
"city_iso": "10",
"continent_geoname_id": 6255147,
"country_geoname_id": 1733045,
"accuracy_radius": 20,
"location": {
"lon": 101.4432,
"lat": 3.0477
}
}
},
"server": {
"ip": "192.168.1.132",
"port": 22
},
"user": {
"name": "root"
},
"credential": {
"username": "root",
"password": "root",
"compromised": true
},
"session": {
"id": "929b8e7f24f61cf8"
},
"logtype": 4002,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"action": "login",
"protocol_name": "TCP",
"protocol_number": "6",
"ssh": {
"local_version": "SSH-2.0-OpenSSH_8.9p1 Ubuntu-3ubuntu0.1",
"remote_version": "SSH-2.0-OpenSSH_9.6p1 Ubuntu-3ubuntu13.11",
"incoming_packet_sequence": 8,
"outgoing_packet_sequence": 8,
"keyalg": "ssh-rsa",
"login_attempts": 1,
"auth_method": "password"
},
"mitre": {
"tactic": "Persistence, Initial Access",
"technique": "Valid Accounts",
"id": "T1078"
},
"related": {
"ip": [
"158.94.46.176",
"192.168.1.132"
],
"user": [
"root"
]
}
}
}
{
"time": 1748074463,
"host": "CiscoolBox",
"source": "TFTP_READ_ATTEMPT",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "22.163.115.179",
"port": 49037,
"geo": {
"continent": "Europe",
"country": "Germany",
"country_iso": "DE",
"city": "Duisburg",
"postal": "47167",
"timezone": "Europe/Berlin",
"as_domain": "continentale.de",
"as_name": "Continentale Krankenversicherung a.G.",
"asn": "AS56919",
"city_geoname_id": 2934691,
"city_iso": "NW",
"continent_geoname_id": 6255148,
"country_geoname_id": 2921044,
"accuracy_radius": 100,
"location": {
"lon": 6.8017,
"lat": 51.5117
}
}
},
"server": {
"ip": "0.0.0.0",
"port": 69
},
"session": {
"id": "bb9fc65c3645ceeb"
},
"logtype": 10002,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"action": "connection",
"protocol_name": "UDP",
"protocol_number": "17",
"tftp": {
"filename": "bootrom.ld",
"opcode": "READ",
"mode": "octet"
},
"mitre": {
"tactic": "Exfiltration",
"technique": "Exfiltration Over Alternative Protocol",
"id": "T1048"
},
"related": {
"ip": [
"22.163.115.179",
"0.0.0.0"
],
"user": []
}
}
}
{
"time": 1748072722,
"host": "CiscoolBox",
"source": "VNC_LOGIN_ATTEMPT",
"sourcetype": "_json",
"event": {
"timezone": "+00:00",
"device": "honeypot",
"client": {
"ip": "192.168.1.123",
"port": 53678
},
"server": {
"ip": "192.168.1.132",
"port": 5900
},
"credential": {
"password": "12345678"
},
"session": {
"id": "be64fd6f5563f951"
},
"logtype": 12002,
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"action": "login",
"status": "failed",
"protocol_name": "TCP",
"protocol_number": "6",
"vnc": {
"client_response": "0835cbd4461cb5d2d4792da86cfc590d",
"client_version": "RFB 003.008",
"encryption_type": "DES",
"server_challenge": "fe5e3254598eb0182e7d9e553377f7dc"
},
"mitre": {
"tactic": "Credential Access",
"technique": "Brute Force",
"id": "T1110"
},
"related": {
"ip": [
"192.168.1.123",
"192.168.1.132"
],
"user": []
}
}
}
Detection section
The following section provides information for those who wish to learn more about the detection capabilities enabled by collecting this intake. It includes details about the built-in rule catalog, event categories, and ECS fields extracted from raw events. This is essential for users aiming to create custom detection rules, perform hunting activities, or pivot in the events page.
Related Built-in Rules
The following Sekoia.io built-in rules match the intake NeroSwarm Honeypot. This documentation is updated automatically and is based solely on the fields used by the intake which are checked against our rules. This means that some rules will be listed but might not be relevant with the intake.
SEKOIA.IO x NeroSwarm Honeypot on ATT&CK Navigator
Account Added To A Security Enabled Group
Detection in order to investigate who has added a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4728)
- Effort: master
Account Removed From A Security Enabled Group
Detection in order to investigate who has removed a specific Domain User in Domain Admins or Group Policy Creator Owners (Security event 4729)
- Effort: master
Backup Catalog Deleted
The rule detects when the Backup Catalog has been deleted. It means the administrators will not be able to access any backups that were created earlier to perform recoveries. This is often being done using the wbadmin.exe tool.
- Effort: intermediate
Computer Account Deleted
Detects computer account deletion.
- Effort: master
Correlation Admin Files Checked On Network Share
Detects requests to multiple admin files on a network share. This could be an attacker performing reconnaissance steps on the system.
- Effort: advanced
Covenant Default HTTP Beaconing
Detects potential Covenant communications through the user-agent and specific urls
- Effort: intermediate
Cryptomining
Detection of domain names potentially related to cryptomining activities.
- Effort: master
DHCP Server Error Failed Loading the CallOut DLL
This rule detects a DHCP server error in which a specified Callout DLL (in registry) could not be loaded.
- Effort: intermediate
DHCP Server Loaded the CallOut DLL
This rule detects a DHCP server in which a specified Callout DLL (in registry) was loaded. This would indicate a succesful attack against DHCP service allowing to disrupt the service or alter the integrity of the responses.
- Effort: intermediate
DNS Server Error Failed Loading The ServerLevelPluginDLL
This rule detects a DNS server error in which a specified plugin DLL (in registry) could not be loaded. This requires the dedicated Windows event provider Microsoft-Windows-DNS-Server-Service.
- Effort: master
Discord Suspicious Download
Discord is a messaging application. It allows users to create their own communities to share messages and attachments. Those attachments have little to no overview and can be downloaded by almost anyone, which has been abused by attackers to host malicious payloads.
- Effort: advanced
Domain Trust Created Or Removed
A trust was created or removed to a domain. An attacker could perform that in order to do lateral movement easily between domains or shutdown the ability of two domains to communicate.
- Effort: advanced
Dynamic DNS Contacted
Detect communication with dynamic dns domain. This kind of domain is often used by attackers. This rule can trigger false positive in non-controlled environment because dynamic dns is not always malicious.
- Effort: master
Exfiltration Domain
Detects traffic toward a domain flagged as a possible exfiltration vector.
- Effort: master
Internet Scanner
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Internet Scanner Target
Detects known scanner IP addresses. Alert is only raised when the scan hits an opened port, on TCP or UDP and group by target address. This could be a very noisy rule, so be careful to check your detection perimeter before activation.
- Effort: master
Koadic MSHTML Command
Detects Koadic payload using MSHTML module
- Effort: intermediate
Microsoft Defender Antivirus History Deleted
Windows Defender history has been deleted. Could be an attempt by an attacker to remove its traces.
- Effort: master
Microsoft Defender Antivirus Tampering Detected
Detection of Windows Defender Tampering, from definitions' deletion to deactivation of parts or all of Defender.
- Effort: advanced
Microsoft Defender Antivirus Threat Detected
Detection of a windows defender alert indicating the presence of potential malware
- Effort: advanced
Nimbo-C2 User Agent
Nimbo-C2 Uses an unusual User-Agent format in its implants.
- Effort: intermediate
Password Change On Directory Service Restore Mode (DSRM) Account
The Directory Service Restore Mode (DSRM) account is a local administrator account on Domain Controllers. Attackers may change the password to gain persistence.
- Effort: intermediate
Possible Replay Attack
This event can be a sign of Kerberos replay attack or, among other things, network device configuration or routing problems.
- Effort: master
Potential Azure AD Phishing Page (Adversary-in-the-Middle)
Detects an HTTP request to an URL typical of the Azure AD authentication flow, but towards a domain that is not one the legitimate Microsoft domains used for Azure AD authentication.
- Effort: intermediate
Potential Bazar Loader User-Agents
Detects potential Bazar loader communications through the user-agent
- Effort: elementary
Potential Lemon Duck User-Agent
Detects LemonDuck user agent. The format used two sets of alphabetical characters separated by dashes, for example "User-Agent: Lemon-Duck-[A-Z]-[A-Z]".
- Effort: elementary
Potential LokiBot User-Agent
Detects potential LokiBot communications through the user-agent
- Effort: intermediate
Process Trace Alteration
PTrace syscall provides a means by which one process ("tracer") may observe and control the execution of another process ("tracee") and examine and change the tracee's memory and registers. Attacker might want to abuse ptrace functionnality to analyse memory process. It requires to be admin or set ptrace_scope to 0 to allow all user to trace any process.
- Effort: advanced
Remote Access Tool Domain
Detects traffic toward a domain flagged as a Remote Administration Tool (RAT).
- Effort: master
Remote Monitoring and Management Software - AnyDesk
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool AnyDesk.
- Effort: master
Remote Monitoring and Management Software - Atera
Detect artifacts related to the installation or execution of the Remote Monitoring and Management tool Atera.
- Effort: master
SEKOIA.IO Intelligence Feed
Detect threats based on indicators of compromise (IOCs) collected by SEKOIA's Threat and Detection Research team.
- Effort: elementary
Sekoia.io EICAR Detection
Detects observables in Sekoia.io CTI tagged as EICAR, which are fake samples meant to test detection.
- Effort: master
Suspicious PROCEXP152.sys File Created In Tmp
Detects the creation of the PROCEXP152.sys file in the application-data local temporary folder. This driver is used by Sysinternals Process Explorer but also by KDU (https://github.com/hfiref0x/KDU) or Ghost-In-The-Logs (https://github.com/bats3c/Ghost-In-The-Logs), which uses KDU. Note - Clever attackers may easily bypass this detection by just renaming the driver filename. Therefore just Medium-level and don't rely on it.
- Effort: advanced
TOR Usage
Detects TOR usage, based on the IP address and the destination port (filtered on NTP). TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
TOR Usage Generic Rule
Detects TOR usage globally, whether the IP is a destination or source. TOR is short for The Onion Router, and it gets its name from how it works. TOR intercepts the network traffic from one or more apps on user’s computer, usually the user web browser, and shuffles it through a number of randomly-chosen computers before passing it on to its destination. This disguises user location, and makes it harder for servers to pick him/her out on repeat visits, or to tie together separate visits to different sites, this making tracking and surveillance more difficult. Before a network packet starts its journey, user’s computer chooses a random list of relays and repeatedly encrypts the data in multiple layers, like an onion. Each relay knows only enough to strip off the outermost layer of encryption, before passing what’s left on to the next relay in the list.
- Effort: master
User Account Created
Detects user creation on windows servers, which shouldn't happen in an Active Directory environment. Apply this on your windows server logs and not on your DC logs. One default account defaultuser0 is excluded as only used during Windows set-up. This detection use Security Event ID 4720.
- Effort: master
User Account Deleted
Detects local user deletion
- Effort: master
Event Categories
The following table lists the data source offered by this integration.
| Data Source | Description |
|---|---|
Network intrusion detection system |
None |
In details, the following table denotes the type of events produced by this integration.
| Name | Values |
|---|---|
| Kind | Alert |
| Category | `` |
| Type | `` |
Transformed Events Samples after Ingestion
This section demonstrates how the raw logs will be transformed by our parsers. It shows the extracted fields that will be available for use in the built-in detection rules and hunting activities in the events page. Understanding these transformations is essential for analysts to create effective detection mechanisms with custom detection rules and to leverage the full potential of the collected data.
{
"message": "{\"time\": 1748052015, \"host\": \"CiscoolBox\", \"source\": \"HTTP_GET\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"user_agent\": {\"original\": \"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36\"}, \"client\": {\"ip\": \"192.168.1.212\", \"port\": 56419, \"geo\": {\"continent\": null, \"country\": null, \"country_iso\": null, \"city\": null, \"postal\": null, \"timezone\": null, \"as_domain\": null, \"as_name\": null, \"asn\": null, \"city_geoname_id\": null, \"city_iso\": null, \"continent_geoname_id\": null, \"country_geoname_id\": null, \"accuracy_radius\": null, \"location\": {\"lon\": null, \"lat\": null}}}, \"server\": {\"ip\": \"192.168.1.132\", \"port\": 443}, \"url\": {\"path\": \"/login\"}, \"http\": {\"request\": {\"method\": \"GET\", \"referrer\": null, \"headers\": {\"useragent\": \"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36\", \"language\": \"en-US,en;q=0.7\"}}, \"response\": {\"status_code\": \"200\"}}, \"tls\": {\"version_protocol\": \"http/1.1\"}, \"user\": {\"name\": null}, \"credential\": {\"compromised\": null}, \"session\": {\"id\": \"518b913f3cf61879\"}, \"language\": \"en-US,en;q=0.7\", \"logtype\": 3000, \"tracking_id\": \"eb2ab4dcad5bfa9908be7f29da14aa81d0f84e8a3cf9396deb477171cd7ca60e\", \"template\": \"openwrt\", \"action\": \"connection\", \"protocol_name\": \"TCP\", \"protocol_number\": \"6\", \"vulnerability\": {\"id\": null, \"description\": null}, \"cmd\": {\"list\": null}, \"crawler\": {\"bot_name\": null, \"bot_category\": null}, \"file\": {\"upload_file\": null, \"mime_type\": null, \"size\": null, \"hash\": {\"sha256\": null}}, \"dns\": {\"type\": null, \"ip\": null, \"nameserver\": null, \"alias\": null, \"mname\": null, \"rname\": null, \"serial\": null, \"refresh\": null, \"retry\": null, \"expire\": null, \"minimum\": null, \"pointer\": null, \"exchange\": null, \"preference\": null, \"text\": null}, \"ssh\": {\"local_version\": null, \"remote_version\": null, \"incoming_packet_sequence\": null, \"outgoing_packet_sequence\": null, \"keyalg\": null, \"login_attempts\": null, \"auth_method\": null}, \"sql\": {\"client_encoding\": null, \"database\": null, \"thread_id\": null, \"hash_type\": null, \"salt\": null}, \"vnc\": {\"client_response\": null, \"client_version\": null, \"encryption_type\": null, \"server_challenge\": null}, \"rdp\": {\"client\": null, \"cookie\": null, \"mstshash\": null}, \"ntp\": {\"request_type\": null, \"request_mode\": null, \"request_version\": null}, \"sip\": {\"headers\": {\"allow\": null, \"call-id\": null, \"contact\": null, \"from\": null, \"cseq\": null, \"max-forwards\": null, \"to\": null, \"via\": null, \"user-agent\": null, \"content-type\": null, \"accept\": null}, \"error\": null}, \"snmp\": {\"version\": null, \"community_string\": null, \"pdu_type\": null, \"request_id\": null, \"variable_bindings\": null}, \"tftp\": {\"filename\": null, \"opcode\": null, \"mode\": null}, \"git\": {\"repo\": null, \"host\": null}, \"mitre\": {\"tactic\": \"Discovery\", \"technique\": \"File and Directory Discovery\", \"id\": \"T1083\"}, \"raw_data\": {\"post_data\": null}, \"related\": {\"ip\": [\"192.168.1.212\", \"192.168.1.132\"], \"user\": [null]}}}",
"event": {
"action": "connection",
"category": [
"network"
],
"code": "3000",
"kind": "Alert",
"provider": "HTTP_GET",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T02:00:15Z",
"destination": {
"address": "192.168.1.132",
"ip": "192.168.1.132",
"port": 443
},
"host": {
"name": "CiscoolBox"
},
"http": {
"request": {
"method": "GET"
},
"response": {
"status_code": 200
}
},
"neroswarm": {
"cmd": "{\"list\":null}",
"session": {
"id": "518b913f3cf61879"
},
"source": {
"geo": {
"accuracy_radius": 0,
"asn": 0
}
},
"template": "openwrt",
"tracking_id": "eb2ab4dcad5bfa9908be7f29da14aa81d0f84e8a3cf9396deb477171cd7ca60e"
},
"network": {
"iana_number": "6",
"protocol": "HTTP",
"transport": "TCP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"192.168.1.132",
"192.168.1.212"
]
},
"source": {
"address": "192.168.1.212",
"ip": "192.168.1.212",
"port": 56419
},
"threat": {
"tactic": {
"name": "Discovery"
},
"technique": {
"id": "T1083",
"name": "File and Directory Discovery"
}
},
"tls": {
"version": "http/1.1"
},
"url": {
"path": "/login"
},
"user_agent": {
"device": {
"name": "Other"
},
"name": "Chrome",
"original": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/136.0.0.0 Safari/537.36",
"os": {
"name": "Windows",
"version": "10"
},
"version": "136.0.0"
}
}
{
"message": "{\"time\": 1748073000, \"host\": \"CiscoolBox\", \"source\": \"NTP_REQUEST\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"148.170.245.211\", \"port\": 33372, \"geo\": {\"continent\": \"Europe\", \"country\": \"Belgium\", \"country_iso\": \"BE\", \"city\": \"Brussels\", \"postal\": \"1000\", \"timezone\": \"Europe/Brussels\", \"as_domain\": \"easyhost.be\", \"as_name\": \"Easyhost BVBA\", \"asn\": \"AS28747\", \"city_geoname_id\": 2800866, \"city_iso\": \"BRU\", \"continent_geoname_id\": 6255148, \"country_geoname_id\": 2802361, \"accuracy_radius\": 20, \"location\": {\"lon\": 4.347, \"lat\": 50.8534}}}, \"server\": {\"ip\": \"0.0.0.0\", \"port\": 123}, \"session\": {\"id\": \"7f08bb08f3c54ba\"}, \"logtype\": 11001, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"action\": \"connection\", \"protocol_name\": \"UDP\", \"protocol_number\": \"17\", \"ntp\": {\"request_type\": \"Symmetric Active\", \"request_mode\": \"1\", \"request_version\": \"3\"}, \"mitre\": {\"tactic\": \"Reconnaissance\", \"technique\": \"Active Scanning\", \"id\": \"T1595\"}, \"related\": {\"ip\": [\"148.170.245.211\", \"0.0.0.0\"], \"user\": []}}}",
"event": {
"action": "connection",
"category": [
"network"
],
"code": "11001",
"kind": "Alert",
"provider": "NTP_REQUEST",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T07:50:00Z",
"destination": {
"address": "0.0.0.0",
"ip": "0.0.0.0",
"port": 123
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"ntp": {
"request_mode": "1",
"request_type": "Symmetric Active",
"request_version": "3"
},
"session": {
"id": "7f08bb08f3c54ba"
},
"source": {
"geo": {
"accuracy_radius": 20,
"as_domain": "easyhost.be",
"as_name": "Easyhost BVBA",
"asn": 0,
"city_geoname_id": "2800866",
"continent_geoname_id": "6255148",
"country_geoname_id": "2802361"
}
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572"
},
"network": {
"iana_number": "17",
"protocol": "NTP",
"transport": "UDP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"0.0.0.0",
"148.170.245.211"
]
},
"source": {
"address": "148.170.245.211",
"geo": {
"city_name": "Brussels",
"continent_name": "Europe",
"country_name": "Belgium",
"location": {
"lat": 50.8534,
"lon": 4.347
},
"timezone": "Europe/Brussels"
},
"ip": "148.170.245.211",
"port": 33372
},
"threat": {
"tactic": {
"name": "Reconnaissance"
},
"technique": {
"id": "T1595",
"name": "Active Scanning"
}
}
}
{
"message": "{\"time\": 1748073209, \"host\": \"CiscoolBox\", \"source\": \"POSTGRES_LOGIN_ATTEMPT\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"8.98.145.113\", \"port\": 55086, \"geo\": {\"continent\": \"North America\", \"country\": \"United States\", \"country_iso\": \"US\", \"timezone\": \"America/Chicago\", \"as_domain\": \"amazon.com\", \"as_name\": \"Amazon.com, Inc.\", \"asn\": \"AS14618\", \"continent_geoname_id\": 6255149, \"country_geoname_id\": 6252001, \"accuracy_radius\": 1000, \"location\": {\"lon\": -97.822, \"lat\": 37.751}}}, \"server\": {\"ip\": \"192.168.1.132\", \"port\": 5432}, \"user\": {\"name\": \"postgres\"}, \"credential\": {\"username\": \"postgres\", \"password\": \"postgres\", \"compromised\": true}, \"session\": {\"id\": \"b6f6512185e4064d\"}, \"logtype\": 20001, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"action\": \"login\", \"status\": \"success\", \"protocol_name\": \"TCP\", \"protocol_number\": \"6\", \"sql\": {\"client_encoding\": \"UTF8\", \"database\": \"postgres\"}, \"mitre\": {\"tactic\": \"Persistence, Initial Access\", \"technique\": \"Valid Accounts\", \"id\": \"T1078\"}, \"related\": {\"ip\": [\"8.98.145.113\", \"192.168.1.132\"], \"user\": [\"postgres\"]}}}",
"event": {
"action": "login",
"category": [
"authentication"
],
"code": "20001",
"kind": "Alert",
"provider": "POSTGRES_LOGIN_ATTEMPT",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T07:53:29Z",
"destination": {
"address": "192.168.1.132",
"ip": "192.168.1.132",
"port": 5432
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"credential": {
"compromised": "true",
"password": "postgres",
"username": "postgres"
},
"session": {
"id": "b6f6512185e4064d"
},
"source": {
"geo": {
"accuracy_radius": 1000,
"as_domain": "amazon.com",
"as_name": "Amazon.com, Inc.",
"asn": 0,
"continent_geoname_id": "6255149",
"country_geoname_id": "6252001"
}
},
"sql": {
"client_encoding": "UTF8",
"database": "postgres"
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572"
},
"network": {
"iana_number": "6",
"protocol": "POSTGRES",
"transport": "TCP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"192.168.1.132",
"8.98.145.113"
],
"user": [
"postgres"
]
},
"source": {
"address": "8.98.145.113",
"geo": {
"continent_name": "North America",
"country_name": "United States",
"location": {
"lat": 37.751,
"lon": -97.822
},
"timezone": "America/Chicago"
},
"ip": "8.98.145.113",
"port": 55086
},
"threat": {
"tactic": {
"name": "Persistence, Initial Access"
},
"technique": {
"id": "T1078",
"name": "Valid Accounts"
}
},
"user": {
"name": "postgres"
}
}
{
"message": "{\"time\": 1748075181, \"host\": \"CiscoolBox\", \"source\": \"RDP_LOGIN_ATTEMPT\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"152.111.92.207\", \"port\": 60892, \"geo\": {\"continent\": \"Asia\", \"country\": \"South Korea\", \"country_iso\": \"KR\", \"timezone\": \"Asia/Seoul\", \"as_domain\": \"uplus.co.kr\", \"as_name\": \"LG DACOM Corporation\", \"asn\": \"AS3786\", \"continent_geoname_id\": 6255147, \"country_geoname_id\": 1835841, \"accuracy_radius\": 200, \"location\": {\"lon\": 126.9741, \"lat\": 37.5112}}}, \"server\": {\"ip\": \"192.168.1.132\", \"port\": 3389}, \"user\": {\"name\": \"admin\"}, \"credential\": {\"username\": \"admin\", \"password\": \"windows123\", \"compromised\": false}, \"session\": {\"id\": \"5a385f4d044f7c0f\"}, \"logtype\": 14003, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"domain\": \"prod\", \"action\": \"login\", \"status\": \"failed\", \"protocol_name\": \"TCP\", \"protocol_number\": \"6\", \"rdp\": {\"client\": \"remina\"}, \"mitre\": {\"tactic\": \"Credential Access\", \"technique\": \"Brute Force\", \"id\": \"T1110\"}, \"related\": {\"ip\": [\"152.111.92.207\", \"192.168.1.132\"], \"user\": [\"admin\"]}}}",
"event": {
"action": "login",
"category": [
"authentication"
],
"code": "14003",
"kind": "Alert",
"provider": "RDP_LOGIN_ATTEMPT",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T08:26:21Z",
"destination": {
"address": "192.168.1.132",
"ip": "192.168.1.132",
"port": 3389
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"credential": {
"compromised": "false",
"password": "windows123",
"username": "admin"
},
"rdp": {
"client": "remina"
},
"session": {
"id": "5a385f4d044f7c0f"
},
"source": {
"geo": {
"accuracy_radius": 200,
"as_domain": "uplus.co.kr",
"as_name": "LG DACOM Corporation",
"asn": 0,
"continent_geoname_id": "6255147",
"country_geoname_id": "1835841"
}
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572"
},
"network": {
"iana_number": "6",
"protocol": "RDP",
"transport": "TCP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"152.111.92.207",
"192.168.1.132"
],
"user": [
"admin"
]
},
"source": {
"address": "152.111.92.207",
"geo": {
"continent_name": "Asia",
"country_name": "South Korea",
"location": {
"lat": 37.5112,
"lon": 126.9741
},
"timezone": "Asia/Seoul"
},
"ip": "152.111.92.207",
"port": 60892
},
"threat": {
"tactic": {
"name": "Credential Access"
},
"technique": {
"id": "T1110",
"name": "Brute Force"
}
},
"user": {
"name": "admin"
}
}
{
"message": "{\"time\": 1748070903, \"host\": \"CiscoolBox\", \"source\": \"SSH_LOGIN_ATTEMPT\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"158.94.46.176\", \"port\": 41958, \"geo\": {\"continent\": \"Asia\", \"country\": \"Malaysia\", \"country_iso\": \"MY\", \"city\": \"Klang\", \"postal\": \"41700\", \"timezone\": \"Asia/Kuala_Lumpur\", \"as_domain\": \"tm.com.my\", \"as_name\": \"TM TECHNOLOGY SERVICES SDN. BHD.\", \"asn\": \"AS4788\", \"city_geoname_id\": 1732905, \"city_iso\": \"10\", \"continent_geoname_id\": 6255147, \"country_geoname_id\": 1733045, \"accuracy_radius\": 20, \"location\": {\"lon\": 101.4432, \"lat\": 3.0477}}}, \"server\": {\"ip\": \"192.168.1.132\", \"port\": 22}, \"user\": {\"name\": \"root\"}, \"credential\": {\"username\": \"root\", \"password\": \"root\", \"compromised\": true}, \"session\": {\"id\": \"929b8e7f24f61cf8\"}, \"logtype\": 4002, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"action\": \"login\", \"protocol_name\": \"TCP\", \"protocol_number\": \"6\", \"ssh\": {\"local_version\": \"SSH-2.0-OpenSSH_8.9p1 Ubuntu-3ubuntu0.1\", \"remote_version\": \"SSH-2.0-OpenSSH_9.6p1 Ubuntu-3ubuntu13.11\", \"incoming_packet_sequence\": 8, \"outgoing_packet_sequence\": 8, \"keyalg\": \"ssh-rsa\", \"login_attempts\": 1, \"auth_method\": \"password\"}, \"mitre\": {\"tactic\": \"Persistence, Initial Access\", \"technique\": \"Valid Accounts\", \"id\": \"T1078\"}, \"related\": {\"ip\": [\"158.94.46.176\", \"192.168.1.132\"], \"user\": [\"root\"]}}}",
"event": {
"action": "login",
"category": [
"authentication"
],
"code": "4002",
"kind": "Alert",
"provider": "SSH_LOGIN_ATTEMPT",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T07:15:03Z",
"destination": {
"address": "192.168.1.132",
"ip": "192.168.1.132",
"port": 22
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"credential": {
"compromised": "true",
"password": "root",
"username": "root"
},
"session": {
"id": "929b8e7f24f61cf8"
},
"source": {
"geo": {
"accuracy_radius": 20,
"as_domain": "tm.com.my",
"as_name": "TM TECHNOLOGY SERVICES SDN. BHD.",
"asn": 0,
"city_geoname_id": "1732905",
"continent_geoname_id": "6255147",
"country_geoname_id": "1733045"
}
},
"ssh": {
"auth_method": "password",
"incoming_packet_sequence": "8",
"keyalg": "ssh-rsa",
"local_version": "SSH-2.0-OpenSSH_8.9p1 Ubuntu-3ubuntu0.1",
"login_attempts": "1",
"outgoing_packet_sequence": "8",
"remote_version": "SSH-2.0-OpenSSH_9.6p1 Ubuntu-3ubuntu13.11"
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572"
},
"network": {
"iana_number": "6",
"protocol": "SSH",
"transport": "TCP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"158.94.46.176",
"192.168.1.132"
],
"user": [
"root"
]
},
"source": {
"address": "158.94.46.176",
"geo": {
"city_name": "Klang",
"continent_name": "Asia",
"country_name": "Malaysia",
"location": {
"lat": 3.0477,
"lon": 101.4432
},
"timezone": "Asia/Kuala_Lumpur"
},
"ip": "158.94.46.176",
"port": 41958
},
"threat": {
"tactic": {
"name": "Persistence, Initial Access"
},
"technique": {
"id": "T1078",
"name": "Valid Accounts"
}
},
"user": {
"name": "root"
}
}
{
"message": "{\"time\": 1748074463, \"host\": \"CiscoolBox\", \"source\": \"TFTP_READ_ATTEMPT\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"22.163.115.179\", \"port\": 49037, \"geo\": {\"continent\": \"Europe\", \"country\": \"Germany\", \"country_iso\": \"DE\", \"city\": \"Duisburg\", \"postal\": \"47167\", \"timezone\": \"Europe/Berlin\", \"as_domain\": \"continentale.de\", \"as_name\": \"Continentale Krankenversicherung a.G.\", \"asn\": \"AS56919\", \"city_geoname_id\": 2934691, \"city_iso\": \"NW\", \"continent_geoname_id\": 6255148, \"country_geoname_id\": 2921044, \"accuracy_radius\": 100, \"location\": {\"lon\": 6.8017, \"lat\": 51.5117}}}, \"server\": {\"ip\": \"0.0.0.0\", \"port\": 69}, \"session\": {\"id\": \"bb9fc65c3645ceeb\"}, \"logtype\": 10002, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"action\": \"connection\", \"protocol_name\": \"UDP\", \"protocol_number\": \"17\", \"tftp\": {\"filename\": \"bootrom.ld\", \"opcode\": \"READ\", \"mode\": \"octet\"}, \"mitre\": {\"tactic\": \"Exfiltration\", \"technique\": \"Exfiltration Over Alternative Protocol\", \"id\": \"T1048\"}, \"related\": {\"ip\": [\"22.163.115.179\", \"0.0.0.0\"], \"user\": []}}}",
"event": {
"action": "connection",
"category": [
"network"
],
"code": "10002",
"kind": "Alert",
"provider": "TFTP_READ_ATTEMPT",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T08:14:23Z",
"destination": {
"address": "0.0.0.0",
"ip": "0.0.0.0",
"port": 69
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"session": {
"id": "bb9fc65c3645ceeb"
},
"source": {
"geo": {
"accuracy_radius": 100,
"as_domain": "continentale.de",
"as_name": "Continentale Krankenversicherung a.G.",
"asn": 0,
"city_geoname_id": "2934691",
"continent_geoname_id": "6255148",
"country_geoname_id": "2921044"
}
},
"tftp": {
"filename": "bootrom.ld",
"mode": "octet",
"opcode": "READ"
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572"
},
"network": {
"iana_number": "17",
"protocol": "TFTP",
"transport": "UDP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"0.0.0.0",
"22.163.115.179"
]
},
"source": {
"address": "22.163.115.179",
"geo": {
"city_name": "Duisburg",
"continent_name": "Europe",
"country_name": "Germany",
"location": {
"lat": 51.5117,
"lon": 6.8017
},
"timezone": "Europe/Berlin"
},
"ip": "22.163.115.179",
"port": 49037
},
"threat": {
"tactic": {
"name": "Exfiltration"
},
"technique": {
"id": "T1048",
"name": "Exfiltration Over Alternative Protocol"
}
}
}
{
"message": "{\"time\": 1748072722, \"host\": \"CiscoolBox\", \"source\": \"VNC_LOGIN_ATTEMPT\", \"sourcetype\": \"_json\", \"event\": {\"timezone\": \"+00:00\", \"device\": \"honeypot\", \"client\": {\"ip\": \"192.168.1.123\", \"port\": 53678}, \"server\": {\"ip\": \"192.168.1.132\", \"port\": 5900}, \"credential\": {\"password\": \"12345678\"}, \"session\": {\"id\": \"be64fd6f5563f951\"}, \"logtype\": 12002, \"tracking_id\": \"b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572\", \"action\": \"login\", \"status\": \"failed\", \"protocol_name\": \"TCP\", \"protocol_number\": \"6\", \"vnc\": {\"client_response\": \"0835cbd4461cb5d2d4792da86cfc590d\", \"client_version\": \"RFB 003.008\", \"encryption_type\": \"DES\", \"server_challenge\": \"fe5e3254598eb0182e7d9e553377f7dc\"}, \"mitre\": {\"tactic\": \"Credential Access\", \"technique\": \"Brute Force\", \"id\": \"T1110\"}, \"related\": {\"ip\": [\"192.168.1.123\", \"192.168.1.132\"], \"user\": []}}}",
"event": {
"action": "login",
"category": [
"authentication"
],
"code": "12002",
"kind": "Alert",
"provider": "VNC_LOGIN_ATTEMPT",
"type": [
"info"
]
},
"@timestamp": "2025-05-24T07:45:22Z",
"destination": {
"address": "192.168.1.132",
"ip": "192.168.1.132",
"port": 5900
},
"host": {
"name": "CiscoolBox"
},
"neroswarm": {
"credential": {
"password": "12345678"
},
"session": {
"id": "be64fd6f5563f951"
},
"tracking_id": "b29a2f994fdaf479ec46efd1afc4fbd5a6be90a44f337cb05b939a95019a3572",
"vnc": {
"client_response": "0835cbd4461cb5d2d4792da86cfc590d",
"client_version": "RFB 003.008",
"encryption_type": "DES",
"server_challenge": "fe5e3254598eb0182e7d9e553377f7dc"
}
},
"network": {
"iana_number": "6",
"protocol": "VNC",
"transport": "TCP"
},
"observer": {
"product": "NeroPot",
"vendor": "NeroSwarm"
},
"related": {
"ip": [
"192.168.1.123",
"192.168.1.132"
]
},
"source": {
"address": "192.168.1.123",
"ip": "192.168.1.123",
"port": 53678
},
"threat": {
"tactic": {
"name": "Credential Access"
},
"technique": {
"id": "T1110",
"name": "Brute Force"
}
}
}
Extracted Fields
The following table lists the fields that are extracted, normalized under the ECS format, analyzed and indexed by the parser. It should be noted that infered fields are not listed.
| Name | Type | Description |
|---|---|---|
@timestamp |
date |
Date/time when the event originated. |
destination.ip |
ip |
IP address of the destination. |
destination.port |
long |
Port of the destination. |
event.action |
keyword |
The action captured by the event. |
event.code |
keyword |
Identification code for this event. |
event.kind |
keyword |
The kind of the event. The highest categorization field in the hierarchy. |
event.provider |
keyword |
Source of the event. |
file.hash.sha256 |
keyword |
SHA256 hash. |
file.mime_type |
keyword |
Media type of file, document, or arrangement of bytes. |
file.path |
keyword |
Full path to the file, including the file name. |
file.size |
long |
File size in bytes. |
host.name |
keyword |
Name of the host. |
http.request.method |
keyword |
HTTP request method. |
http.request.referrer |
keyword |
Referrer for this HTTP request. |
http.response.status_code |
long |
HTTP response status code. |
neroswarm.cmd |
keyword |
Shell Session Commands |
neroswarm.crawler.bot_category |
keyword |
Crawler Identification Bot Category |
neroswarm.crawler.bot_name |
keyword |
Crawler Identification Bot Name |
neroswarm.credential.compromised |
keyword |
Credential Access Compromised |
neroswarm.credential.password |
keyword |
Credential Access Password |
neroswarm.credential.username |
keyword |
Credential Access Username |
neroswarm.dns.alias |
keyword |
DNS Alias |
neroswarm.dns.exchange |
keyword |
DNS Exchange |
neroswarm.dns.expire |
keyword |
DNS Expire |
neroswarm.dns.ip |
keyword |
DNS IP |
neroswarm.dns.minimum |
keyword |
DNS Minimum |
neroswarm.dns.mname |
keyword |
DNS Mname |
neroswarm.dns.nameserver |
keyword |
DNS Nameserver |
neroswarm.dns.pointer |
keyword |
DNS Pointer |
neroswarm.dns.preference |
keyword |
DNS Preference |
neroswarm.dns.refresh |
keyword |
DNS Refresh |
neroswarm.dns.retry |
keyword |
DNS Retry |
neroswarm.dns.rname |
keyword |
DNS Rname |
neroswarm.dns.serial |
keyword |
DNS Serial |
neroswarm.dns.text |
keyword |
DNS Text |
neroswarm.dns.type |
keyword |
DNS Type |
neroswarm.ntp.request_mode |
keyword |
NTP Request Mode |
neroswarm.ntp.request_type |
keyword |
NTP Request Type |
neroswarm.ntp.request_version |
keyword |
NTP Request Version |
neroswarm.rdp.client |
keyword |
RDP Client |
neroswarm.rdp.cookie |
keyword |
RDP Cookie |
neroswarm.rdp.mstshash |
keyword |
RDP Mstshash |
neroswarm.session.id |
keyword |
Service Tracking ID |
neroswarm.sip.error |
keyword |
SIP Error |
neroswarm.sip.headers.accept |
keyword |
SIP Headers Accept |
neroswarm.sip.headers.allow |
keyword |
SIP Headers Allow |
neroswarm.sip.headers.call-id |
keyword |
SIP Headers Call-ID |
neroswarm.sip.headers.contact |
keyword |
SIP Headers Contact |
neroswarm.sip.headers.content-type |
keyword |
SIP Headers Content-Type |
neroswarm.sip.headers.cseq |
keyword |
SIP Headers CSeq |
neroswarm.sip.headers.from |
keyword |
SIP Headers From |
neroswarm.sip.headers.max-forwards |
keyword |
SIP Headers Max-Forwards |
neroswarm.sip.headers.to |
keyword |
SIP Headers To |
neroswarm.sip.headers.user-agent |
keyword |
SIP Headers User-Agent |
neroswarm.sip.headers.via |
keyword |
SIP Headers Via |
neroswarm.snmp.community_string |
keyword |
SNMP Community String |
neroswarm.snmp.pdu_type |
keyword |
SNMP PDU Type |
neroswarm.snmp.request_id |
keyword |
SNMP Request ID |
neroswarm.snmp.variable_bindings |
keyword |
SNMP Variable Bindings |
neroswarm.snmp.version |
keyword |
SNMP Version |
neroswarm.source.geo.accuracy_radius |
integer |
GeoIP AS Info Accuracy Radius |
neroswarm.source.geo.as_domain |
keyword |
GeoIP AS Info AS Domain |
neroswarm.source.geo.as_name |
keyword |
GeoIP AS Info AS Name |
neroswarm.source.geo.asn |
integer |
GeoIP AS Info ASN |
neroswarm.source.geo.city_geoname_id |
keyword |
GeoIP AS Info City Geoname ID |
neroswarm.source.geo.continent_geoname_id |
keyword |
GeoIP AS Info Continent Geoname ID |
neroswarm.source.geo.country_geoname_id |
keyword |
GeoIP AS Info Country Geoname ID |
neroswarm.sql.client_encoding |
keyword |
SQL Client Encoding |
neroswarm.sql.database |
keyword |
SQL Database |
neroswarm.sql.hash_type |
keyword |
SQL Hash Type |
neroswarm.sql.salt |
keyword |
SQL Salt |
neroswarm.sql.thread_id |
keyword |
SQL Thread ID |
neroswarm.ssh.auth_method |
keyword |
SSH Auth Method |
neroswarm.ssh.incoming_packet_sequence |
keyword |
SSH Incoming Packet Sequence |
neroswarm.ssh.keyalg |
keyword |
SSH Keyalg |
neroswarm.ssh.local_version |
keyword |
SSH Local Version |
neroswarm.ssh.login_attempts |
keyword |
SSH Login Attempts |
neroswarm.ssh.outgoing_packet_sequence |
keyword |
SSH Outgoing Packet Sequence |
neroswarm.ssh.remote_version |
keyword |
SSH Remote Version |
neroswarm.template |
keyword |
AI Template |
neroswarm.tftp.filename |
keyword |
TFTP Filename |
neroswarm.tftp.mode |
keyword |
TFTP Mode |
neroswarm.tftp.opcode |
keyword |
TFTP Opcode |
neroswarm.tracking_id |
keyword |
Threat Tracking ID |
neroswarm.vnc.client_response |
keyword |
VNC Client Response |
neroswarm.vnc.client_version |
keyword |
VNC Client Version |
neroswarm.vnc.encryption_type |
keyword |
VNC Encryption Type |
neroswarm.vnc.server_challenge |
keyword |
VNC Server Challenge |
neroswarm.vulnerability.description |
text |
CWE Vulnerability Description |
neroswarm.vulnerability.id |
keyword |
CWE Vulnerability ID |
network.iana_number |
keyword |
IANA Protocol Number. |
network.protocol |
keyword |
Application protocol name. |
network.transport |
keyword |
Protocol Name corresponding to the field iana_number. |
observer.product |
keyword |
The product name of the observer. |
observer.vendor |
keyword |
Vendor name of the observer. |
source.geo.city_name |
keyword |
City name. |
source.geo.continent_code |
keyword |
Continent code. |
source.geo.continent_name |
keyword |
Name of the continent. |
source.geo.country_name |
keyword |
Country name. |
source.geo.location |
geo_point |
Longitude and latitude. |
source.geo.timezone |
keyword |
Time zone. |
source.ip |
ip |
IP address of the source. |
source.port |
long |
Port of the source. |
threat.tactic.name |
keyword |
Threat tactic. |
threat.technique.id |
keyword |
Threat technique id. |
threat.technique.name |
keyword |
Threat technique name. |
tls.version |
keyword |
Numeric part of the version parsed from the original string. |
url.path |
wildcard |
Path of the request, such as "/search". |
user.name |
keyword |
Short name or login of the user. |
user_agent.original |
keyword |
Unparsed user_agent string. |
For more information on the Intake Format, please find the code of the Parser, Smart Descriptions, and Supported Events here.